Hey all,
This is another post in the BADministration series where we’ll be exploring Acronis Backup from an offensive standpoint. As always, before going further, one thing I would like to make clear – this is not an Acronis issue or vulnerability. This post instead discusses features and architecture issues, similar to spanning a trusted domain to a less-trusted network. Also once again, a shout-out to CherryDarkness for all the help. Video is at the bottom.
BADministration – https://github.com/ThunderGunExpress/BADministration
Gaining access to the backup solution can be critical during an offensive engagement. Any account with access to a backup share (or server) can mount images to read information from the backed up filesystem, and by extension, local system hashes. These shares or servers can provide an attacker with a potential escalation path, or at a minimum, privileged information about the organization’s security and administrative configurations. However, this post is not about leveraging backup shares, it’s about leveraging the backup server itself!
Other related offsec management application posts:
Application Segmentation
Similar to other administration applications like AV and NMS, backup servers and clients share a trusted relationship. As defenders, it’s not enough to protect critical networks or systems as singular objects; instead, we need to defend their associations as well. For example, if we have a critical OT network, we need to understand all external associations, how they could be maliciously leveraged, and defend them appropriately.
Application segmentation isn’t a new topic, but it’s one that often goes unnoticed. As exploitation of modern apps and OSes becomes more difficult, attackers will increasingly look to inject themselves into the administration chain. For OT networks (and IT aspects), it’s my opinion that the old approach of assessing externally accessible dataflows for known technical vulnerabilities is no longer sufficient. We need to extend our network assessment and segmentation approach to domains, applications, and platforms. As application segmentation is a standalone post, I’ll link it here when it gets done.

For Acronis specific controls, access to the management server is controlled by three Windows’ local groups created at installation.

In my testing, removing the compromised account from the Acronis Centralized Admins group nullified all BADministration modules (all Acronis management access as well). Furthermore, it appears you can create organizational units to segment administration, but if you’re planning on going down that road I strongly recommend looking at the Acronis Admin Guide instead, rather than listening to some rando on the internet. As an exposure takeaway, if one of the following is compromised, all associated clients will be compromised by extension:
- Acronis Management Server
- Any account with local administrator access to the Acronis Management Server
- Any account with membership to the local Acronis Centralized Admins group on the Acronis Management Server
And also, here is an interesting tidbit that probably warrants further research for another day (comes with the Acronis installation).

Current Acronis Modules

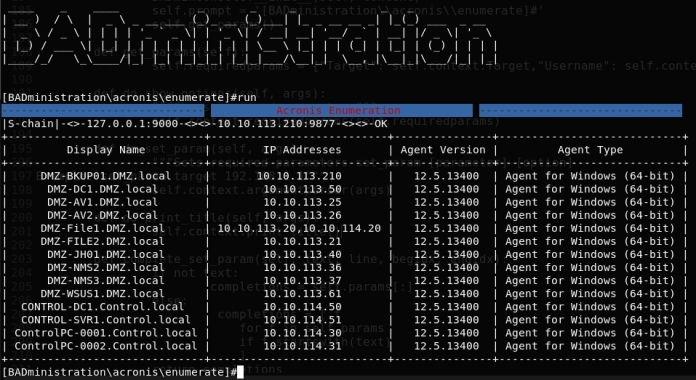
- enumerate – Enumerates all Acronis clients
- list_policy – Lists all backup policies. Initially constructed to check if the BADministration policy was successfully deleted after RCE; however, it could be modified to display share path and other interesting backup details.
- remove_policy – Removes the hardcoded “CPL_Backup” policy.
- client_command – Will attempt to back up c:\users\default\ntuser.dat to c:\users\public\thisisatemp while executing the specified BADministration command as a pre-backup command and subsequently deleting the thisisatemp directory as a post-backup command. However, a word of warning, the post-backup command doesn’t always execute correctly, sometimes there will be an empty c:\users\public\thisisatemp directory left behind.
Testing was done on Acronis Backup 12.5. Also, we took a run at a new UI via cmd. This is a humble side project for Cherry and I with learning being one of our primary goals, I’m sure there are quite a few bugs so be kind with your roasting.
Video!
Sorry for the constant choppy highlighting!