Hey all,
Lately I’ve been playing around with MSI files as an all-in-one phishing package. I feel that MSIs are moderately trusted when it comes to downloadable files. Couple this with the ability to introduce some logic and I think MSIs can be a great way to avoid common security controls while shooting for that initial foothold during an engagement.
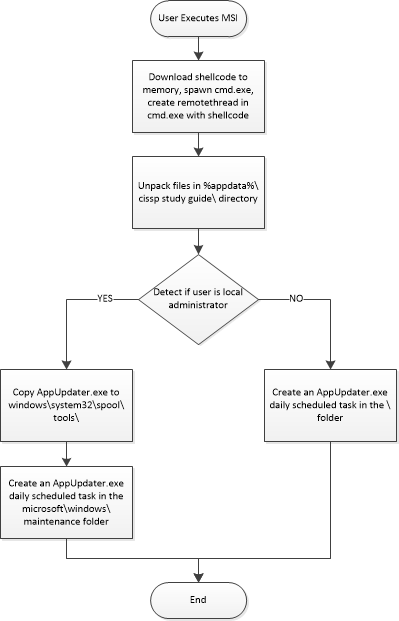
Personally, I feel when targeting users of high infosec awareness it’s best to bring the target to you and make them want to download your software. I like to bundle a bunch of publicly available legitimate tools with one or two of my custom written files … never embed cleartext shellcode, always grab it from a web server, dns, or whatever. This post follows ThunderMSI, a faux CISSP study guide that performs a series of actions depending on the user’s privilege level.
Recommended Read – Wixsharp Managed Setup
How to Defend
- Be skeptical when downloading software. It might be a good idea to have an auditing VM dedicated to vet software before installing on your primary machine.
- A good HIDS should be able to flag or detect several of the suspicious actions in this PoC. For example, a well written MSI shouldn’t be writing an exe to system32 or creating scheduled tasks in Windows sub-directories.
- Monitor processes for network IO. It’s not a good thing if cmd.exe or powershell.exe is consistently generating unexpected network traffic.
Overview
ThunderMSI is a C# program using wix and wixsharp that builds into a single .MSI file. It contains nothing that should be flagged as malicious; however, there are some WINAPI calls (createremotethread) that might trigger advanced endpoint solutions.