Hey all,
Lately I’ve been neglecting my CTF posts so I could put some time into OutlookToolbox, a C# DLL that uses COM to target Outlook in the background. Additionally, I put together a Cobalt Strike Aggressor script to assist with the execution of OutlookToolbox, both of which can be found at the repository here – https://github.com/ThunderGunExpress/OutlookToolbox.
This is a quick and dirty post which will cover the features. Later, I plan on creating another post which further explores potential use cases of OutlookToolbox.
Mandatory
- Only use for good.
- I have not done extensive testing with this tool, use at your own risk. I recommend testing OutlookToolbox on a replica of your target first.
- The Aggressor script uses several brm (file and/or directory remove) function calls which can bulldoze entire directories if input is not sanitized correctly. I’ve tried to iron out all the issues, but still, I would put OutlookToolbox in a non-critical directory like C:\Users\Public\Documents just to be safe.
What it Does
- Lists folders in Outlook (Inbox, Sent Items, Conversation History, Joe’s Custom Folder … )
- Exports target folder to a CSV File
- Enumerate targets using the GAL
- Download specific messages
- Sends an email on behalf of the target user
How to Prevent
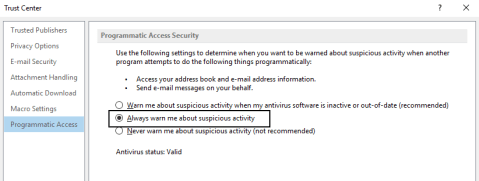
Configure Outlook’s programmatic access security to report on suspicious activity – MS link. Email encryption will cause several of these functions not to work, not a bad idea.