Hey all,
Recently we put together an attack demonstration targeting our simulated lab OT network using a few of the tools that have been explored on this site. The video is linked at the bottom.
Some of the techniques employed are nasty, especially the Outlook hooking and WSUS angle. Regardless of the nastiness level, all these techniques are publicly available and in some cases, have actively been used against our networks. However there is good news, everything explored in this demonstration can be detected and thwarted with relative ease. Additionally, I’m going to link the ATT&CK identifiers in brackets where applicable.
Scenario
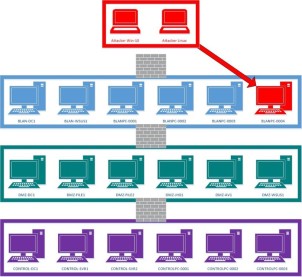
In this demonstration, our adversary is APT123 and is masquerading as Causenoevil.com, a local cybersecurity consulting company. They are targeting M2Generation.com, a power generation company. APT123 wants to take full control of OT systems and perform a DoS attack.
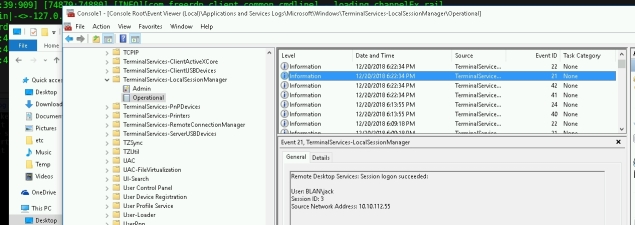
APT123 has a Cobalt Strike (S0154) team server and an attacking Windows 10 system accessible on the internet. During the demonstration we truncate the file transfer process and a few other non-sexy activities. Just a FYI, if you see a Windows 10 machine with a skull and crossbones, that is APT123’s system.
Initial Foothold
APT123 gains a initial foothold on the M2Generation enterprise network using a malicious macro inside an xls document (T1193, T1064, T1203). In the demonstration we take a look at the macro and see that it spawns a “legitimate” iexplore.exe process which automatically browses to causenoevil.com. Additionally, hidden from view the macro also spawns an illegitimate iexplore.exe process while downloading and injecting shellcode via createremotethread. The macro code structure is pretty standard but it has been modified with our custom stager to bypass standard AV and traffic inspection.
Attackers love malicious macros and are actively using them. One or two clicks away from code execution with a widely used application garners attention. However, as defenders we have a plethora of options to protect our networks against this angle, to list a few:
- Windows Defender ASR Rules
- Block Office Macros from the Internet
- Endpoint Security Solutions
- Security Awareness Training