Hey all,
I hope all is well and everyone is enjoying their Summer2019! It’s that time of year again, conference season. I’m looking forward to Las Vegas to enjoy some delicious beers, put on about five pounds, and feel woefully inadequate due to all the badass intelligent people I hopefully will meet! I’m pretty out-of-the-loop when it comes to these things, so if there are any must attend meetups or anything like that, please let me know on twitter.
This post is about BADministration and leveraging McAfee ePO from an offensive standpoint. Before going further, one thing I would like to make clear – this is not a McAfee issue or vulnerability. This post instead discusses features and architecture issues, similar to spanning a trusted domain to a less-trusted network. Also once again, a shout-out to CherryDarkness for all the help.
BADministration – https://github.com/ThunderGunExpress/BADministration
Other related offsec management application posts:
How to Defend
In the last post, application segmentation was briefly discussed and is also applicable to this type of attack. I’m hoping to eventually find time to do an in-depth post about application segmentation and aggregate relevant and better written links here. Until then, I’ll touch on a few McAfee specific controls which would prevent this type of approach.
To stop attackers from leveraging ePO to gain access to target accessible agents, the most effective approach (imo) is implementing role-based access control. Below we see the default permissions of the Group Admins template. In the video, if security personnel assigned the compromised account to this group instead of administrative access, the entire exploitation chain would be rendered null.


To establish a SYSTEM session on target ePO clients, BADministration needs to check in a malicious package, create a client task, and run that task on target systems. The image below is an example of an AD account being assigned ePO administrative privileges. This critical mis-configuration will be explored in the video later in this post.

If an attacker gains access to the standalone ePO admin account, any account with administrative ePO access, or SYSTEM level access to the ePO server; consider all clients exploited by association. This is when application segmentation comes into play which will be discussed in a standalone post at a later date.
Current McAfee Modules
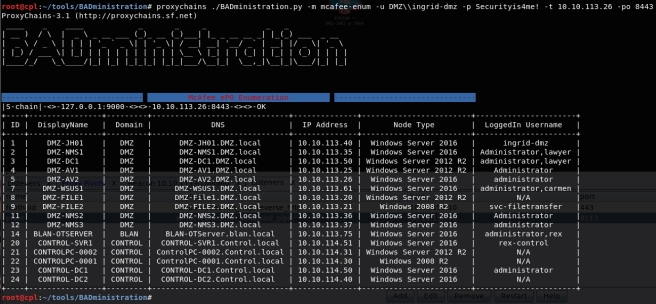
- mcafee-enum – Enumerates all ePO clients
- mcafee-listpackages – Lists all ePO packages
- mcafee-removepackage – Removes ePO package by ID
- mcafee-uploadpackage – Uploads package created with ePO Endpoint Deployment Kit
- mcafee-createtask – Creates client deploy task by package ID and taskname
- mcafee-removetask – Removes client deploy task by taskname
- mcafee-listtasks – Lists all client tasks
- mcafee-runtask – Runs client deploy task targeting given systems (“all” = all ePO clients)
Also, I realize the entire BADministration interface is getting noisy, I intend to take care of that shortly.
References
- McAfee Python API Module
- McAfee ePO Endpoint Deployment Kit (EEDK)
- Troubleshooting note – ambiguous error message with ePOSign.exe requires msvcp71.dll from the .NET Framework SDK Version 1.1 or via alternative methods. McAfee relevant post.
No Payload Left Behind
Note, when deploying a payload via an ePO client task the exe (or whatever) is not deleted from disk. BADministration does not clean this up, that is on you.

Video

In this video we’re going to steal Ingrid-DMZ’s credentials (again!), who also happens to be an AV Administrator. With those credentials, we’ll interface and enumerate all ePO clients, including systems in different trust zones – an application segmentation no-no. With ePO administrative access, we’ll deploy a malicious reverse TCP payload using the ePO Endpoint Deployment Kit and BADministration. Referencing the package, a client task is created and ran on target systems providing SYSTEM access across the entire organization. To cap the demonstration we’ll remove the malicious package and client task.