Hey all,
Uninspired title, I know. Anyways, this is a simple post exploring the use of Impacket and SOCKS with Kerberos tickets, finishing with Rubeus sprinkled in for a cheesy UAC bypass. Throughout this post we’ll be looking at the following tools:
- Impacket
- Rubeus
- Proxychains
- Dnsmasq
- Ticket_Converter
Impacket, Proxychains, and Kerberos
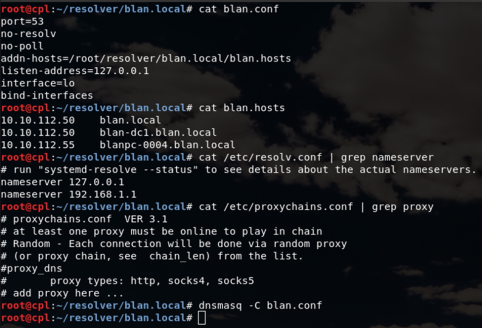
This has always been a bit clunky for me due to name resolution. In order for Kerberos authentication to work properly we need to be able to resolve the FQDN of target hosts and the KDC. Proxychains uses a predefined DNS server to resolve targets if the proxy_dns configuration is enabled. To get name resolution working, I attempted to take both the /etc/hosts and /usr/lib/proxychains3 route, neither of which worked. The issues looked pretty simple to troubleshoot, but instead I opted to use dnsmasq with a custom configuration as a localhost resolver. It keeps everything nice and organized and bypasses the need to send name requests over proxychains. The screenshot below describes the configurations I used.
This video quickly demonstrates putting everything together to generate a TGT for Jack and using wmiexec to establish a session over proxychains.
TGTDeleg with Rubeus
UAC is not a security boundary, it’s not even a road bump if we have credentials. In the video above we use Jack’s cleartext credentials to generate a TGT to demonstrate the use of Impacket with Kerberos tickets. However, if we don’t have credentials things can get a bit more tricky and we might have to stop by UACMe. This post will take a different route and explore tgtdeleg with Rubeus which was inspired by Kekeo. Harmjoy does a real nice write up, I strongly recommend checking it out.
In the video below we start out in a medium integrity context and use tgtdeleg to grab the domain user’s TGT, convert it to a ccache format using Ticket_Converter, and finish the PoC by establishing a high integrity psexec.py session. Pretty simple. And before you all condemn me to shadow realm for writing executables everywhere, know that my next post will look at COM hijacking with something like this to shrink the footprint.