Hey all,
Recently we put together an attack demonstration targeting our simulated lab OT network using a few of the tools that have been explored on this site. The video is linked at the bottom.
Some of the techniques employed are nasty, especially the Outlook hooking and WSUS angle. Regardless of the nastiness level, all these techniques are publicly available and in some cases, have actively been used against our networks. However there is good news, everything explored in this demonstration can be detected and thwarted with relative ease. Additionally, I’m going to link the ATT&CK identifiers in brackets where applicable.
Scenario
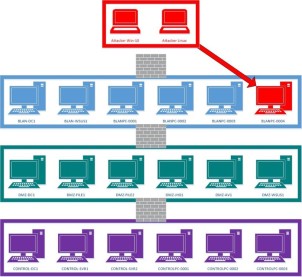
In this demonstration, our adversary is APT123 and is masquerading as Causenoevil.com, a local cybersecurity consulting company. They are targeting M2Generation.com, a power generation company. APT123 wants to take full control of OT systems and perform a DoS attack.
APT123 has a Cobalt Strike (S0154) team server and an attacking Windows 10 system accessible on the internet. During the demonstration we truncate the file transfer process and a few other non-sexy activities. Just a FYI, if you see a Windows 10 machine with a skull and crossbones, that is APT123’s system.
Initial Foothold
APT123 gains a initial foothold on the M2Generation enterprise network using a malicious macro inside an xls document (T1193, T1064, T1203). In the demonstration we take a look at the macro and see that it spawns a “legitimate” iexplore.exe process which automatically browses to causenoevil.com. Additionally, hidden from view the macro also spawns an illegitimate iexplore.exe process while downloading and injecting shellcode via createremotethread. The macro code structure is pretty standard but it has been modified with our custom stager to bypass standard AV and traffic inspection.
Attackers love malicious macros and are actively using them. One or two clicks away from code execution with a widely used application garners attention. However, as defenders we have a plethora of options to protect our networks against this angle, to list a few:
- Windows Defender ASR Rules
- Block Office Macros from the Internet
- Endpoint Security Solutions
- Security Awareness Training
Enumerating OT Networks and Targeting a Privileged User
With a foothold on the M2Generation enterprise network (via BLAN\Jack) but no direct path to being able to laterally move, APT123 turns to Jack’s Outlook for information. APT123 finds OT information in Jack’s inbox along with a trusted OT system administrator – Rex. Exchanged between Rex and Jack is an inventory spreadsheet with critical OT information (T1114), including details of poor application segmentation via WSUS.
APT123 downloads the OT inventory spreadsheet, embeds a malicious macro, and proceeds to send it to BLAN\Rex on behalf of BLAN\Jack. Rex opens the spreadsheet from Jack, a trusted user, and executes the malicious macro.
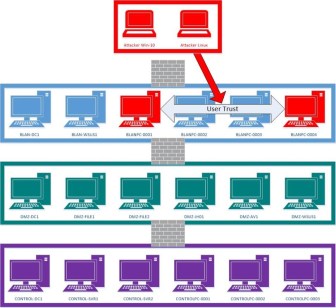
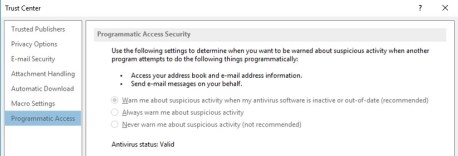
Outlook hooking is nothing new. The specific tool used in this demonstration was OutlookToolbox; however, from an offensive standpoint there are so many different tools and approaches to gain access to an exploited user’s emails. Securing this approach is outside the scope of this blog post but for OutlookToolbox specifically, setting Object Model Guard will detect and thwart this type of attack.
Leveraging WSUS to Breach the IT/OT Boundary
With access to BLAN\Rex’s system, APT123 proceeds to find privileged OT information in Rex’s Sent Items Outlook folder. Enumerating Rex’s domain group membership, APT123 also discovers that Rex is a member of the WSUS Admins group. Recall that the OT inventory spreadsheet indicated that all systems, IT and OT, connect to BLAN-WSUS1 to acquire Windows updates, an example of poor application segmentation.
APT123 proceeds to deploy and approve a malicious update to BLAN-WSUS1 and waits for the applied group policy to automatically download and execute the malicious update on client systems (T1072). In the demonstration the malicious package used is the signed psexec.exe with command line arguments which calls bitsadmin to download a malicious executable hosted on BLAN-WSUS1. Once downloaded to each of the WSUS clients, psexec completes the exploitation process by running the malicious executable.
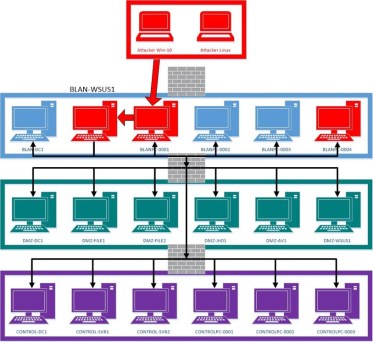
Leveraging applications or solutions to laterally move throughout the network is an burgeoning offensive area of research. Attackers and offensive professionals are finding new and sophisticated approaches to leverage existing solutions to escalate privileges and gain access to sensitive networks.
This specific example was a technique developed by Yves Le Provost and Romain Coltel in 2017. In the demonstration we used a C# rewrite of the powershell WSUSPendu.
As OT security folk, we need to think beyond the traditional network segmentation to include domain, application, and platform segmentation. In my opinion, any internet accessible networks like the enterprise or BLAN, should be treated as breached. Implementing solutions like multi-factor authentication at the IT/OT boundary is especially potent.
For the demonstration, M2Generation exercised poor application segmentation. Having a downstream WSUS server would have made this attack more difficult. A patch management program which included testing of all prospective updates would have also potentially thwarted this type of attack. Additionally, APT123 used psexec to download and execute a malicious executable. Several security solutions could have detected and potentially rejected this process including traffic inspection and endpoint security solutions.
Video