Hey all,
It’s been a while! Lately, I’ve been looking for something similar to browser pivoting but for Chrome. I went down a deep rabbit hole using Headless Chrome, Selenium, Puppeteer, and a few others I cannot remember. I was able to remotely control Chrome on an exploited system but was unable to get it to a point where I felt there was something worthwhile to post. That being said, I do think there is opportunity with Chrome Devtools; a post for another day I suppose.
In this post, I’m going to explore public information that shows how to modify a system to allow multiple remote desktop (RDP) sessions on workstation Operating Systems like Windows 10 and 7. This opens the door to establish RemoteApp connections to a system which already has an active console session. With leveraging RemoteApp, the devil is in the details, so in later posts I’m going to explore potential engagement use cases.
How to Defend
Remote desktop is an action which is virtually always initiated by another user. Windows generates audit logs specifically for RDP sessions which can be used to potentially trigger alerts or investigation. In my opinion, security administrators should be looking for remote desktop sessions as attackers often leverage RDP to gain graphical access to exploited systems.
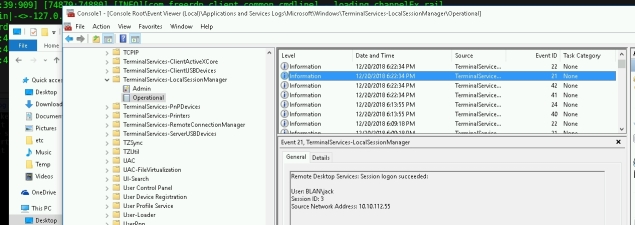
Just a thought, as an end user I also like the idea of creating a task that generates a popup or an email if a remote desktop connection is initiated.
RemoteApp
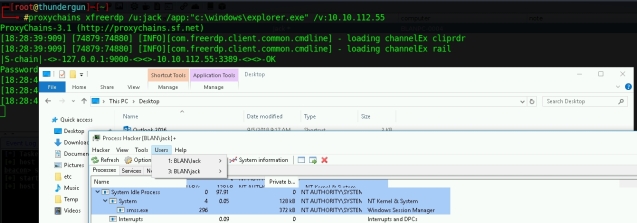
RemoteApp is a solution that graphically provides a remote application using RDP and virtual channels. Offensively, RemoteApp has been leveraged for lateral movement but I think it also has additional potential. From what I have seen most remote desktop clients support RemoteApp including xfreerdp.
![]()
However, by default, Windows workstations will not allow RemoteApp or concurrent RDP session. There are a two hurdles we need to clear before we get to this point, as follows:
- Patch C:\Windows\System32\Termsrv.dll to Allow Concurrent Sessions
- Set HKLM\Software\Microsoft\Windows NT\CurrentVersion\Terminal Server\TSAppAllowList\fDisabledAllowList to 1
Patching Termsrv.dll
Running the xfreerdp command above with an unmodified termsrv.dll will result in the following.
No bueno. If we wanted to RDP into a system without a console session we would wait for the user to logoff. So what we can do is patch c:\windows\system32\termsrv.dll to allow multiple concurrent sessions. Check this out.
Termsrv.dll Version |
Original Hex String |
Modified Hex String |
10.0.17134.1 |
8B 99 3C 06 00 00 8B B9 38 06 00 00 |
B8 00 01 00 00 89 81 38 06 00 00 90 |
10.0.16299.15 |
39 81 3C 06 00 00 0F 84 B1 7D 02 00 |
B8 00 01 00 00 89 81 38 06 00 00 90 |
10.0.15063.0 |
39 81 3C 06 00 00 0F 84 53 71 02 00 |
B8 00 01 00 00 89 81 38 06 00 00 90 |
10.0.10586.0 |
39 81 3C 06 00 00 0F 84 3F 42 02 00 |
B8 00 01 00 00 89 81 38 06 00 00 90 |
10.0.10240.16384 |
39 81 3C 06 00 00 0F 84 73 42 02 00 |
B8 00 01 00 00 89 81 38 06 00 00 90 |
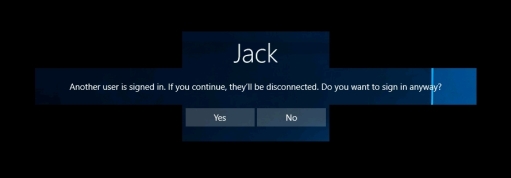
Having patched termsrv.dll with the hex string above, multiple concurrent RDP sessions as other user accounts should now be allowed.
However, if we attempt to RDP to a system as a user with an existing console session, we’ll seize that session. In order to gain graphical access to applications under the context of the user with that console session, we’ll use RemoteApp. When attempting to make a RemoteApp connection using xfreerdp we see the following message.
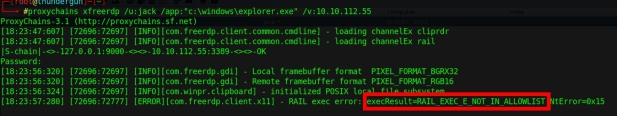
To remedy this, set the following registry DWORD to 1
HKLM\Software\Microsoft\Windows NT\CurrentVersion\Terminal Server\TSAppAllowList\fDisabledAllowList
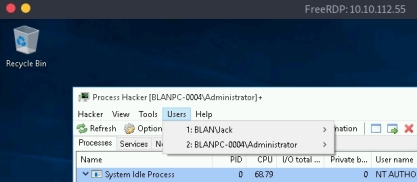
As seen below, trying to open explorer.exe as a RemoteApp now works, while the initial console session goes untouched. Mildly interesting, we can also open child windows through that initial RemoteApp session … very cool.
Code
While it’s not difficult to do this manually, I did create a tool that automates the entire patching process. However, at this time, I’m not going to post it. It’s not that this angle is particularly devastating; instead, I don’t feel too keen publishing a tool that modifies system32 files. If I do decide to publish the code, I’ll post it here.

10.0.17763.437
39 81 3C 06 00 00 0F 84 3B 2B 01 00
B8 00 01 00 00 89 81 38 06 00 00 90
LikeLike